How to decrypt ESP packet in Ipsec
Encryption is good thing when you send your traffic on public network, but sometimes we may need to decrypt packet to troubleshoot the issues and need to see what is going on under the hood.
Here, I am going to explain how to decode the ESP packet using Wireshark
You can see in below image that after phase2 negotiation, data is getting encapsulated using ESP header
(Note: I am using FortiGate firewall here but it would be same process for different vendors as well provided you need to collect authentication and encryption parameters)

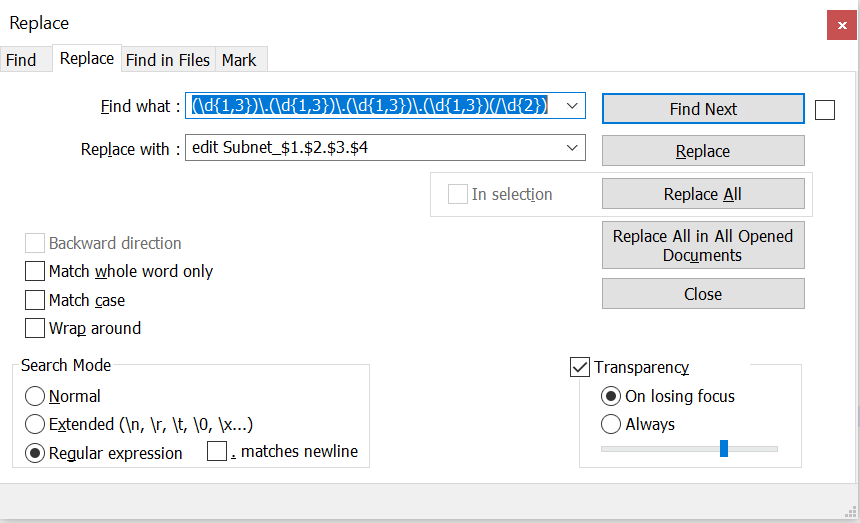
=>In Wireshark navigate to edit -> preferences -> protocol -> esp.
=>As per image, enable the last 3 checkboxes and select "edit" next to ESP SAs

==>Create two entries for the incoming and outgoing SA
==>We need add information obtained from the VPN tunnel list in each line

==>Save the changes
Here, I am going to explain how to decode the ESP packet using Wireshark
You can see in below image that after phase2 negotiation, data is getting encapsulated using ESP header
(Note: I am using FortiGate firewall here but it would be same process for different vendors as well provided you need to collect authentication and encryption parameters)

=>In Wireshark navigate to edit -> preferences -> protocol -> esp.
=>As per image, enable the last 3 checkboxes and select "edit" next to ESP SAs

==>Create two entries for the incoming and outgoing SA
==>We need add information obtained from the VPN tunnel list in each line

==>Save the changes


Comments
Post a Comment